Configuring Virtual Server Authentication Methods
Authentication ensures that
the user is who he or she claims to be. More powerful authentication
methods such as Kerberos ensure that the e-mail server is authenticated
in addition to the user. Encryption ensures that only the recipient for
whom a message is intended can read it.
Authentication
Exchange supports three
methods of user authentication. These are anonymous authentication,
basic authentication, and Integrated Windows Authentication.
Anonymous Authentication
This is the most
common method used for Internet communication and provides limited
access to specific public folders and directory information. Anonymous
authentication is supported by all clients and is used to allow users to
access unsecured content in public folders.
Basic Authentication
Exchange performs
simple challenge and response authentication by requiring that users
enter their user name, domain name, and password to gain access to
mailbox data. Most client computers support basic authentication. This
method provides the simplest level of security.
Important
Basic
authentication sends a user’s name and password as clear text.
Therefore, it is insecure. Basic authentication should not be used
unless there is no alternative or unless the entire TCP/IP session is
encrypted. |
Integrated Windows Authentication
This
method offers security, efficient communication, and transparency. You
can use Integrated Windows Authentication when you have Windows-based
clients that do not use encryption. This method uses Kerberos for
clients running Windows 2000 Server or later, and new technology local
area network (LAN) manager (NTLM) for Windows clients that are not
running Active Directory. When you use Integrated Windows
Authentication, the password is sent as an encrypted value.
Encryption
Encryption scrambles
the contents of an e-mail message into a code that can only be read by
the person who has the key to decode it on his or her computer.
Authentication does not encrypt message data. Therefore, to make your
data truly secure, you should encrypt e-mail messages transferred
between the client and the server. Because TLS and SSL encrypt the
entire TCP/IP session between the client and the server, the session is
secure even if you chose a logon authentication method, such as basic
authentication, that does not encrypt the user name and password.
HTTP, POP3, IMAP4, and
NNTP virtual servers can use SSL encryption. SMTP virtual servers use
TLS, which is a development of SSL. To use encryption, a virtual server
must have a certificate issued by a trusted CA.
Tip
Remember
that encryption scrambles the message. It is not an authentication
method and does not authenticate the user. Remember also that encryption
can be specified on a virtual server only if basic authentication is
enabled. Finally, remember that encryption can be implemented only if a
certificate is obtained. Some dialog boxes let you check the encryption
setting before you obtain the certificate, but this has no effect until
the certificate is installed. |
Other Authentication Methods
Some POP3 and IMAP4 clients use Simple Authentication and Security Layer (SASL)
authentication. This authentication method uses Kerberos or NTLM to
authenticate hosts. SASL can be specified on POP3 and IMAP4 virtual
servers on back-end Exchange Server 2003 servers.
You can specify
digest authentication on HTTP virtual servers. This authenticates
Windows domain servers rather than users. The settings on the Exchange
virtual server (the default HTTP virtual server) also let you specify
Microsoft .NET Passport authentication.
Supported Authentication Methods
Available
authentication methods can vary, depending both upon the type of
virtual server and upon whether the Exchange server is configured as a
back-end or a front-end server. Table 1 gives the details.
Table 1. Supported Authentication Methods
| Virtual server protocol | Exchange server configuration | Supported authentication methods |
|---|
| POP3 and IMAP4 | Back-end | Basic
SASL |
| HTTP | Back-end | Anonymous
Basic
Digest
Integrated Windows Authentication
.NET Password (Exchange virtual server only) |
| NNTP and SMTP | Back-end and front-end | Anonymous
Basic
Integrated Windows Authentication |
| POP3 and IMAP4 | Front-end | Basic (cannot be changed) |
| HTTP | Front-end | Anonymous
Basic
Digest
.NET Password (Exchange virtual server only) Integrated Windows Authentication (Exchange virtual server only) |
Encryption can be
configured on virtual servers on both back-end and front-end Exchange
servers. Typically, encryption is configured on front-end servers that
connect to the Internet. TLS encryption can be used on SMTP virtual
servers, and SSL encryption on all other types of virtual servers. Both
types of encryption require a certificate.
Configuring Client Access to Virtual Server Protocols
Exchange Server
2003 supports HTTP and WebDAV to provide enhanced functionality for HTTP
clients retrieving and manipulating information in Web storage systems.
You can also configure an HTTP virtual server to support OWA and allow
clients to access e-mail, calendar information, shared applications, and
any content in the public folder store, simply and efficiently by using
a Web browser.
IMAP4 clients can access
mail in an Exchange mailbox without downloading the entire mailbox to a
specific computer. Exchange uses NNTP to enable Outlook users to
participate in online discussions over the Internet. Exchange also
enables users running client applications that support NNTP to access
newsgroup public folders on computers running Exchange.
Exchange
allows POP3 clients to access user inboxes on Exchange. However, POP3
users cannot access other public or private folders. POP3 is not
intended to provide full manipulation of mail on the server. Although
messages can be left on the server, mail is usually downloaded to a
user’s computer and then deleted.
To configure POP3 and IMAP4
clients, you need to create a mailbox-enabled user, specify account
information on the client, and set per-user options.
Practice: Obtaining, Installing, and Associating a Certificate for an IMAP4 Virtual Server on a Front-End Exchange Server
This procedure is used to
obtain, associate, and install an encryption certificate on the default
IMAP4 virtual server on the front-end Exchange server, Server02. The
same procedure can be used to obtain, install, and associate a
certificate on the following virtual servers:
An IMAP4 virtual server on a back-end Exchange server
A POP3 virtual server on either a front-end or a back-end Exchange server
An NNTP virtual server on either a front-end or a back-end Exchange server
An SMTP virtual server on either a front-end or a back-end Exchange server
To obtain, install,
and associate a certificate on an HTTP virtual server on either a
front-end or a back-end Exchange server, you need to access the Web
Server Certificate Wizard by using the IIS Manager console rather than
Exchange System Manager.
To obtain, install, and associate a certificate, perform the following ssteps:
1. | Start Exchange System Manager.
|
2. | Navigate to Administrative Groups\First Administrative Group\Servers\Server02\Protocols\IMAP4.
|
3. | Right-click Default IMAP4 Virtual Server, and then click Pause.
|
4. | Right-click Default IMAP4 Virtual Server, and then click Properties.
|
5. | On the Access tab, click Certificate.
|
6. | To
request a new certificate, complete the Web Server Certificate Wizard.
When prompted, select the Create A New Certificate option. Because there
is a CA in your domain, you can obtain the certificate immediately.
|
7. | Click Apply to save your settings.
|
8. | To install the certificate, click Certificate again.
|
9. | Complete the Web Server Certificate Wizard again. This time, select Assign An Existing Certificate when prompted.
|
10. | To associate the certificate and require a secure channel, click Communication on the Access tab.
|
11. | Click Require Secure Channel.
|
12. | If 128-bit encryption is supported on the computer hosting the IMAP4 virtual server, click Require 128-bit Encryption.
|
13. | Click OK to close the virtual server Properties dialog box.
|
14. | Restart the virtual server.
|
Note
You
do not need to obtain a certificate every time you want to enable
encryption on a virtual server. If you have obtained a certificate for
one virtual server on your Exchange server, you can use the Web Server
Certificate Wizard to assign it to other virtual servers. |
Practice: Configuring Authentication
This procedure is the same
for all virtual servers, except for the options that can be set. For
the HTTP default virtual server, you use the IIS Manager console to
access the Authentication sheet through the Directory Security tab of
the Exchange Properties box, but otherwise the procedure is identical.
Exercise 1: Configure Authentication on Virtual Servers on a Back-End Exchange Server
To configure authentication, perform the following steps:
1. | Start Exchange System Manager.
|
2. | Navigate to Administrative Groups\First Administrative Group\Servers\Server01\Protocols.
|
3. | Expand HTTP, NTTP, POP3, IMAP4, and SMTP.
|
4. | Right-click any virtual server except the Exchange virtual server (the HTTP default virtual server), and then click Pause.
|
5. | Right-click the paused virtual server, and then click Properties.
|
6. | On the Access tab, click Authentication.
|
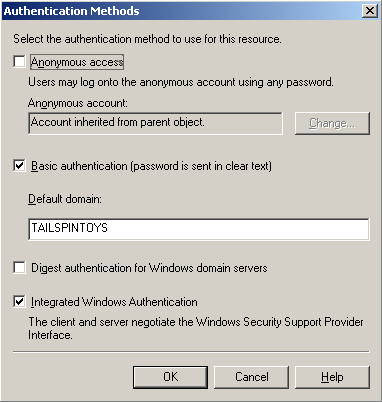
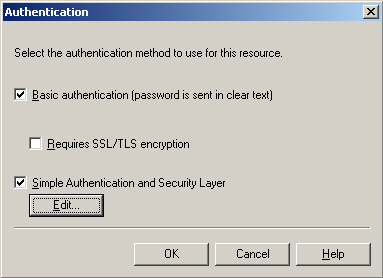
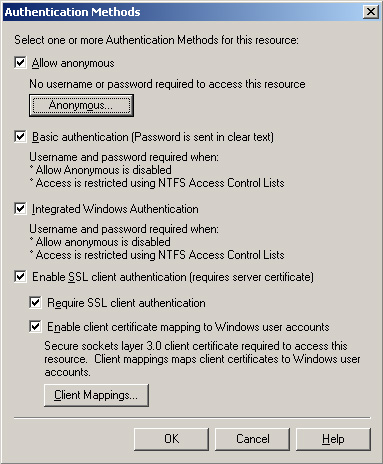
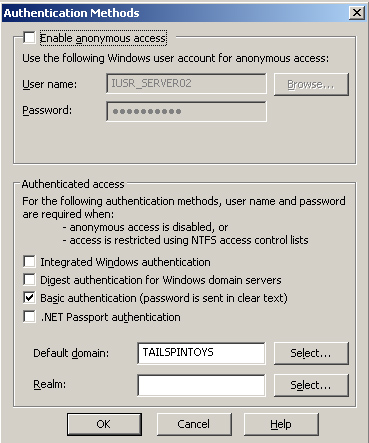
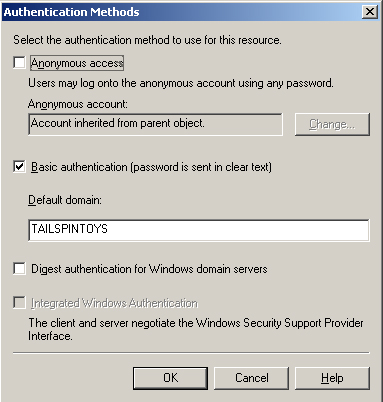
7. | Specify the authentication settings. Figures 2 through 5 show the available options.
|
8. | Click OK to close the virtual server Properties dialog box.
|
9. | Restart the virtual server.
|
Exercise 2: Configure Authentication on the Default HTTP Virtual Server on a Front-End Exchange Server
The purpose of this
exercise is to describe the use of the IIS Manager console to configure
authentication settings on a default HTTP virtual server. The procedure
also illustrates the difference between HTTP virtual servers on a
back-end and on a front-end Exchange server.
1. | Start the IIS Manager console on Server02.
|
2. | Expand Internet Information Services\Server02\Web Sites\Default Web Site \Exchange.
|
3. | Right-click Default Web Site, and then click Pause.
|
4. | Right-click Exchange, and then click Properties.
|
5. | In the Authentication And Access Control section on the Directory Security tab, click Edit.
|
6. | Configure the settings as required. As shown in Figure 6,
Integrated Windows Authentication and .NET Passport authentication are
available on an Exchange virtual server on both front-end and back-end
Exchange servers.
However, on an additional HTTP server on a front-end Exchange server, these options are not available. Figure 7 shows the authentication settings available in this case.
|
7. | Click OK to close the Authentication dialog box.
|
8. | Click OK to close the Exchange Properties dialog box.
|
9. | Restart the default Web site.
|
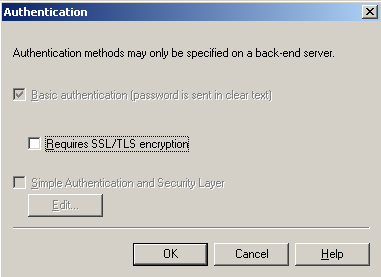
Exercise 3: Examine Authentication Settings on a POP3 Virtual Server on a Front-End Exchange Server
The purpose of this
exercise is to examine the Authentication dialog box on a POP3 virtual
server on a front-end Exchange server. The Authentication dialog box on
an IMAP4 virtual server on a front-end Exchange server looks exactly the
same.
To examine authentication settings, perform the following steps:
1. | Start Exchange System Manager.
|
2. | Navigate to Administrative Groups\First Administrative Group\Servers\Server02\Protocols\POP3.
|
3. | Right-click Default POP3 Virtual Server, and then click Properties.
|
4. | On the Access tab, click Authentication.
|
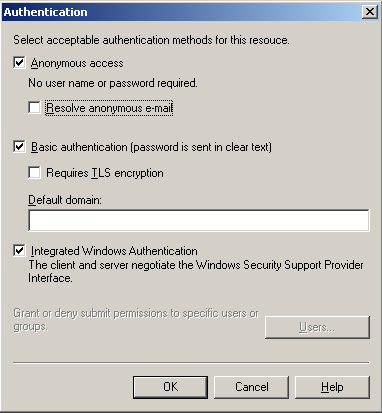
5. | The Authentication dialog box is shown in Figure 8.
Note that on a front-end server, basic authentication is specified and
cannot be changed. The only configuration possible is to enable
encryption.
|
6. | Click OK to close the virtual server dialog box. |